Security Incident Update: ioTube Bridge Exploit and Recovery Roadmap

Executive Summary
On February 21, 2026, the IoTeX team identified and transitioned to emergency response following a security breach affecting ioTube, the IoTeX multi-chain bridge. The exploit was isolated specifically to the Ethereum-side. We are providing this comprehensive report to outline what happened, the status of funds, and our path forward for recovery and compensation. Our forensic analysis indicates this was a sophisticated, professional operation with possible connections to prior high-profile DeFi exploits. Full attribution details will be included in the post-mortem report.
What is Safe
First and foremost, we want to clarify the scope of this incident to reassure our community:
- IoTeX L1 Chain is Safe: The IoTeX Layer 1 chain, its consensus mechanism, and all native smart contracts were NOT compromised.
- User Assets on IoTeX & Exchanges are Safe: Your IOTX tokens on the IoTeX chain and within centralized exchanges are unaffected.
- Isolated Exploit: The breach was isolated strictly to ioTube's Ethereum-side bridge contracts. Bridge contracts on other chains like BSC and Base were not affected.
The Incident: Root Cause & Technical Breakdown
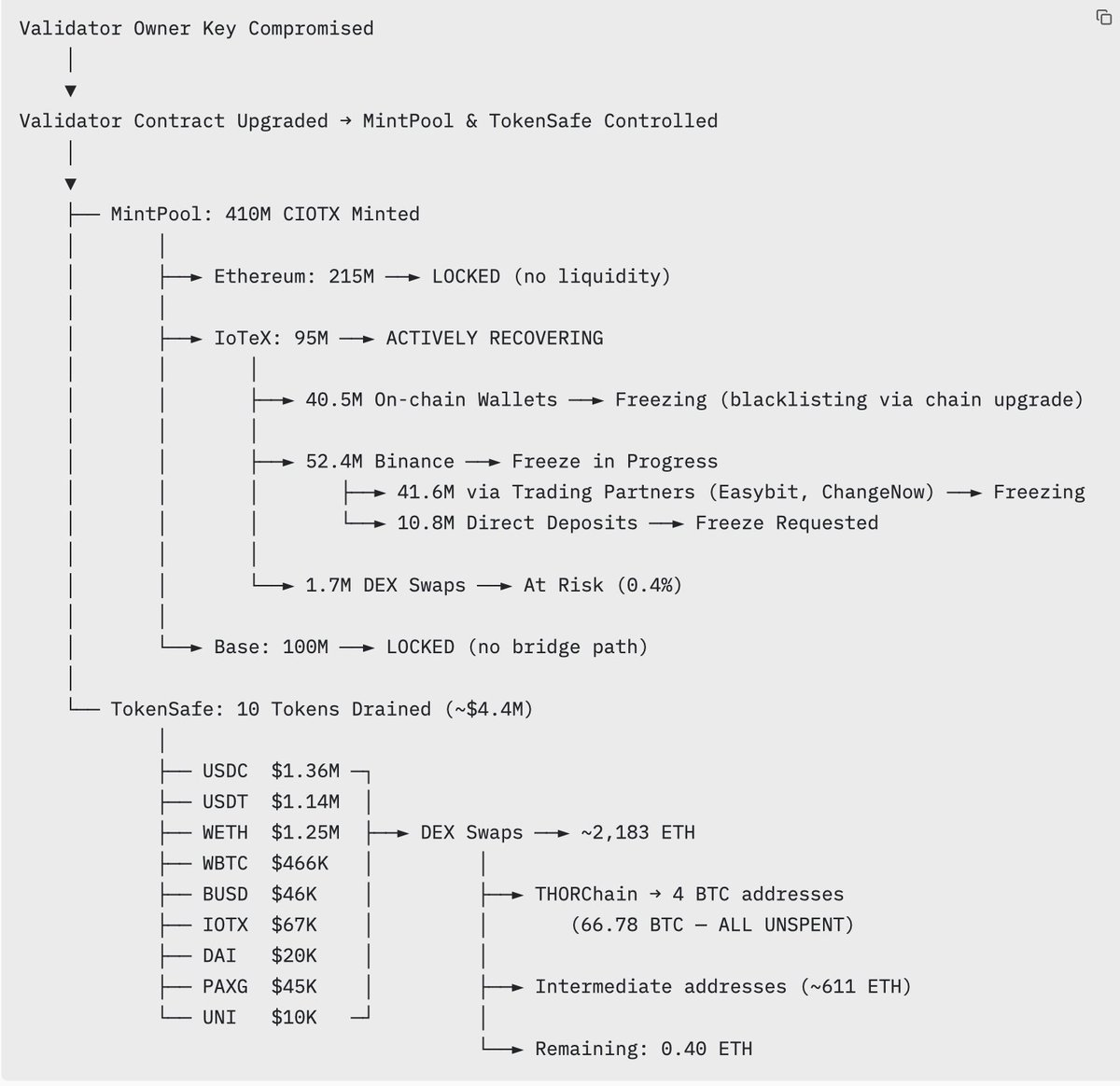
The attack targeted the Ethereum-side of the ioTube bridge through a sophisticated four-step chain:
- Validator Key Compromise: The owner account of the Validator contract on Ethereum was compromised, granting the attacker administrative control.
- Malicious Upgrade: The attacker used this access to upgrade the Validator contract to a malicious version that bypassed all signature and validation checks.
- Contract Takeover: With the validator layer subverted, the attacker took control of the MintPool (token minting) and TokenSafe (reserve assets).
- Asset Drainage: The attacker minted 410M CIOTX and drained approximately $4.4M in various tokens from the bridge reserves.
Current Asset Status & Recovery Efforts
We detected the incident within hours and took immediate action to contain the damage. Our on-chain tracing confirms that the vast majority of stolen assets are already secured:
Part A: 410M CIOTX (MintPool)
The attacker minted 410M CIOTX. Through our rapid response protocol, over 86% of all minted tokens are already locked or being frozen — assets we can secure directly through our own chain-level controls. An additional 12.8% (52.4M IOTX) has been traced to Binance, where we are actively working with Binance and trading partners to freeze. Only 0.4% (1.7M) was swapped on DEX and is considered at risk.
- Ethereum & Base (315M CIOTX): These are completely locked with no liquidity or bridge path.
- IoTeX Chain (95M IOTX): Actively Recovering. Full on-chain tracing is complete. Of the 95M:
- 40.5M remains in attacker wallets — We have identified 29 attacker-controlled addresses on the IoTeX chain and are blacklisting all of them via a chain-level patch. At this moment, we are distributing a patch to chain delegates.
- 52.4M was deposited to Binance — of which 41.6M was routed through trading partners (Easybit, ChangeNow, etc.). We are actively working with Binance and these trading partners to freeze all deposited funds.
1.7M was swapped on DEX — already converted to other tokens. This is the only portion considered at risk, representing just 0.4% of total minted CIOTX.

Part B: Bridge Reserves (TokenSafe)
The attacker converted stolen reserve tokens (including USDC, USDT, WBTC, WETH and other assets) into approximately 2,183 ETH. Of this, approximately 1,572 ETH was bridged to Bitcoin via THORChain, with the remainder dispersed across intermediate Ethereum addresses under active monitoring.
- Status: We have identified 4 Bitcoin addresses holding a total of 66.78 BTC.
- 12V7jhcPnqnGbRFMasSW2CZVBd8qpvUgAK
- 16xusPKLMyqK68SkhfXDtic6AJPDi51tqh
- 1PN2BoHU4buDQWcrNHk9T9NBA2qX8oyYEc
- 135oSa2fobTxtHtm5dwTREDyRY2o1DG1Aw
- Monitoring: As of this report, all BTC remains unspent. These addresses are flagged and under continuous 24/7 monitoring by our team and analytics partners.

Immediate Actions & Resumption Timeline
Our team is working around the clock to restore full services:
- IoTeX L1 Chain: We are starting to distribute patch to chain delegates now; once we have enough patched delegates online, consensus and normal operations will be resumed automatically.
- Exchange Activity: We anticipate withdrawals will resume within 24–48 hours, with deposit functionality following shortly thereafter.
- Community AMA: We will host a community AMA for more details within 24–48 hours.
- Compensation plan: A detailed compensation plan for affected bridge users will be published within 48 hours.
- ioTube Bridge: Bridge operations will remain suspended across all chains until a full, independent security audit is completed. We will also expedite the implementation and roll out of IIP-55.
- Legal & Forensics: We have engaged law enforcement and top-tier on-chain analytics firms. Attacker addresses have been flagged on Etherscan as 0x6487B5006904f3Db3C4a3654409AE92b87eD442f (lablled as Fake_Phishing2054654 on etherscan).
- White-hat Bounty: On-chain message will be sent to attacker offering a white-hat bounty for voluntary return of funds.
Our Commitment to Users
The security of our community’s assets is our highest priority. We are fully committed to making affected users whole:
- Compensation: A detailed compensation plan for affected bridge users will be published within 48 hours.
- Interim Support: Bridge-back requests will be processed manually on a case-by-case basis during this period.
- Transparency: We will host a community AMA with our founding team within the next 24-48 hours.
The Path Forward: Hardening Our Security
This incident is a turning point that has driven us to implement one of the most resilient, multi-layered security frameworks for our cross-chain infrastructure:
- Rigorous Re-Audits: ioTube will remain paused until a full, independent security audit is completed and all vulnerabilities are remediated.
- Decentralized Governance: We are introducing Multi-signature and 24-hour Time-lock controls to eliminate single points of failure. We will also expedite the implementation and roll out of IIP-55, a governance proposal to decentralize bridge validation through a multi-party validator set.
- Intelligent Safeguards: New per-transaction and daily volume limits are being integrated to proactively contain risks.
- Security Bug Bounty: We are launching an expanded Bug Bounty program to collaborate with the global white-hat community in securing our ecosystem.
We thank the IoTeX community for your patience and continued support as we navigate this recovery together.
The IoTeX Team
